Security and scalability are core concerns in system design.
Before building distributed or microservices-based systems, it’s important to clearly understand authentication, authorization, and stateless services—concepts that are often confused but fundamentally different.
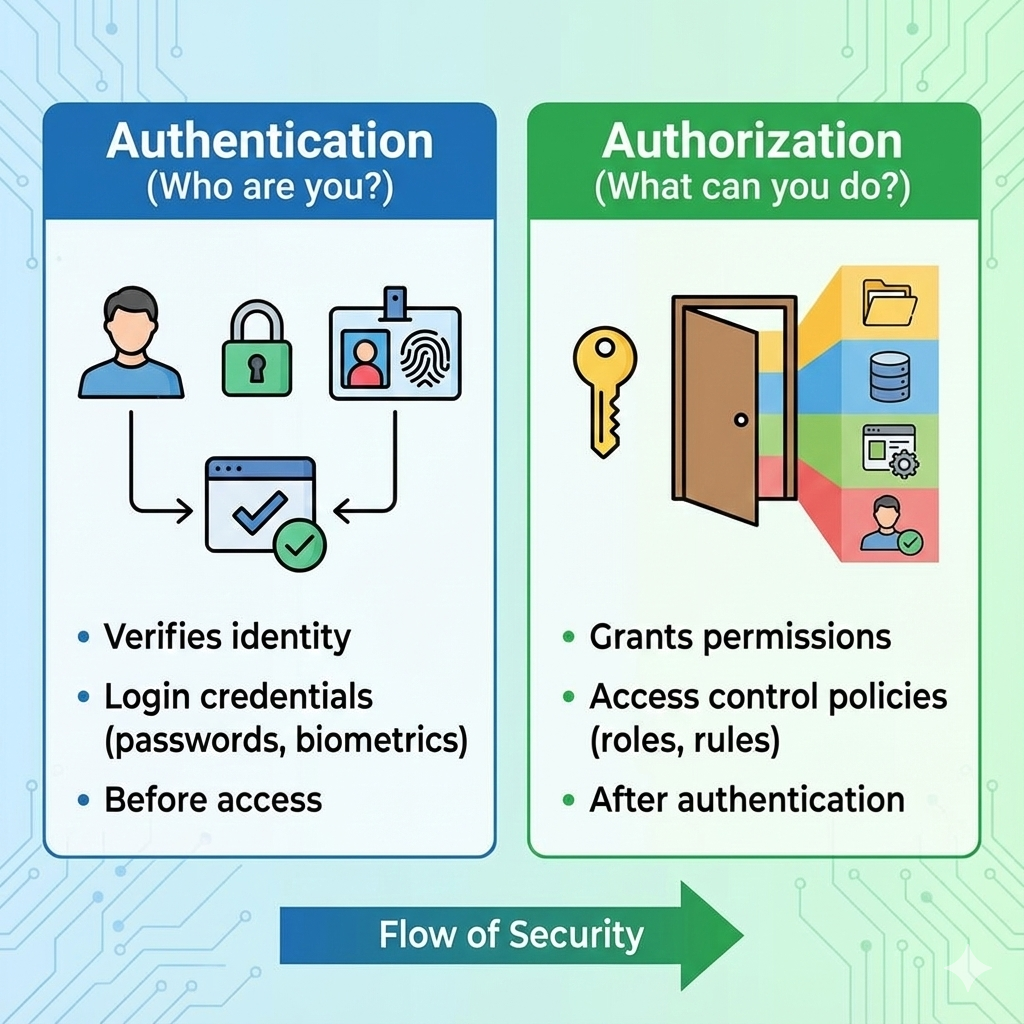
Authentication vs Authorization
Authentication
Authentication answers the question:
“Who are you?”
It verifies the identity of a user or system.
Examples:
- Username and password login
- Login via Google or GitHub
- API key validation
Authorization
Authorization answers the question:
“What are you allowed to do?”
It determines permissions after authentication.
Examples:
- A normal user can view data but cannot delete it
- An admin can create, update, and delete resources
Key Rule:
👉 Authentication always comes before authorization.
Common Authentication Mechanisms
1. Session-Based Authentication
- Server stores session data
- Client stores a session ID (usually in cookies)
- Server checks session on every request
Pros: Simple
Cons: Hard to scale across multiple servers
2. Token-Based Authentication (JWT)
- Server issues a signed token after login
- Client sends token with each request
- Server validates token without storing session state
Pros: Scalable, stateless
Cons: Token revocation is harder
Common Use: REST APIs and microservices
3. OAuth 2.0
- Delegated authorization protocol
- Used when third-party apps access user data
Example:
“Login with Google” or allowing an app to access your GitHub profile.
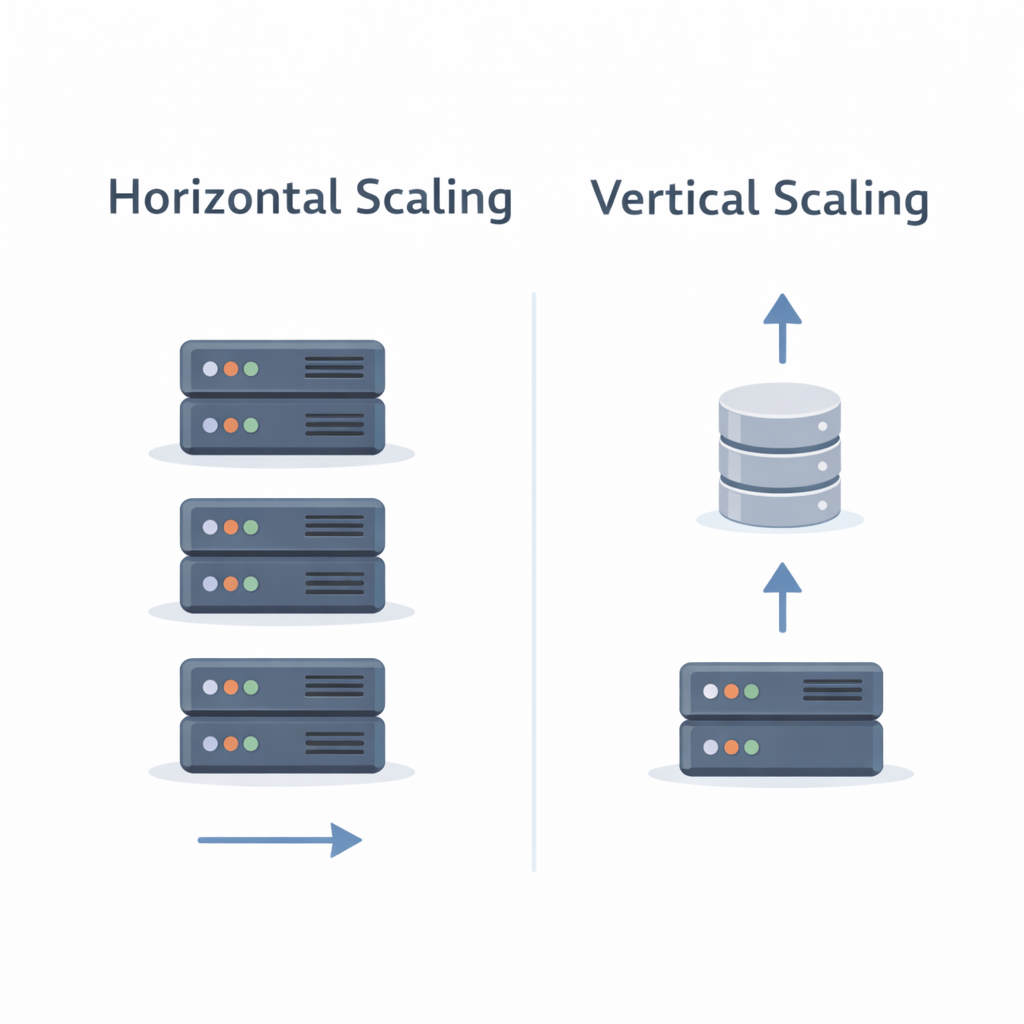
Stateless vs Stateful Services
Stateful Services
- Server maintains client state between requests
- Example: Session stored in server memory
Problems:
- Hard to scale horizontally
- Requires sticky sessions or shared storage
Stateless Services
- Each request contains all required information
- No server-side session storage
Example:
JWT token sent with every request
Benefits:
- Easy horizontal scaling
- Better fault tolerance
- Simple load balancing
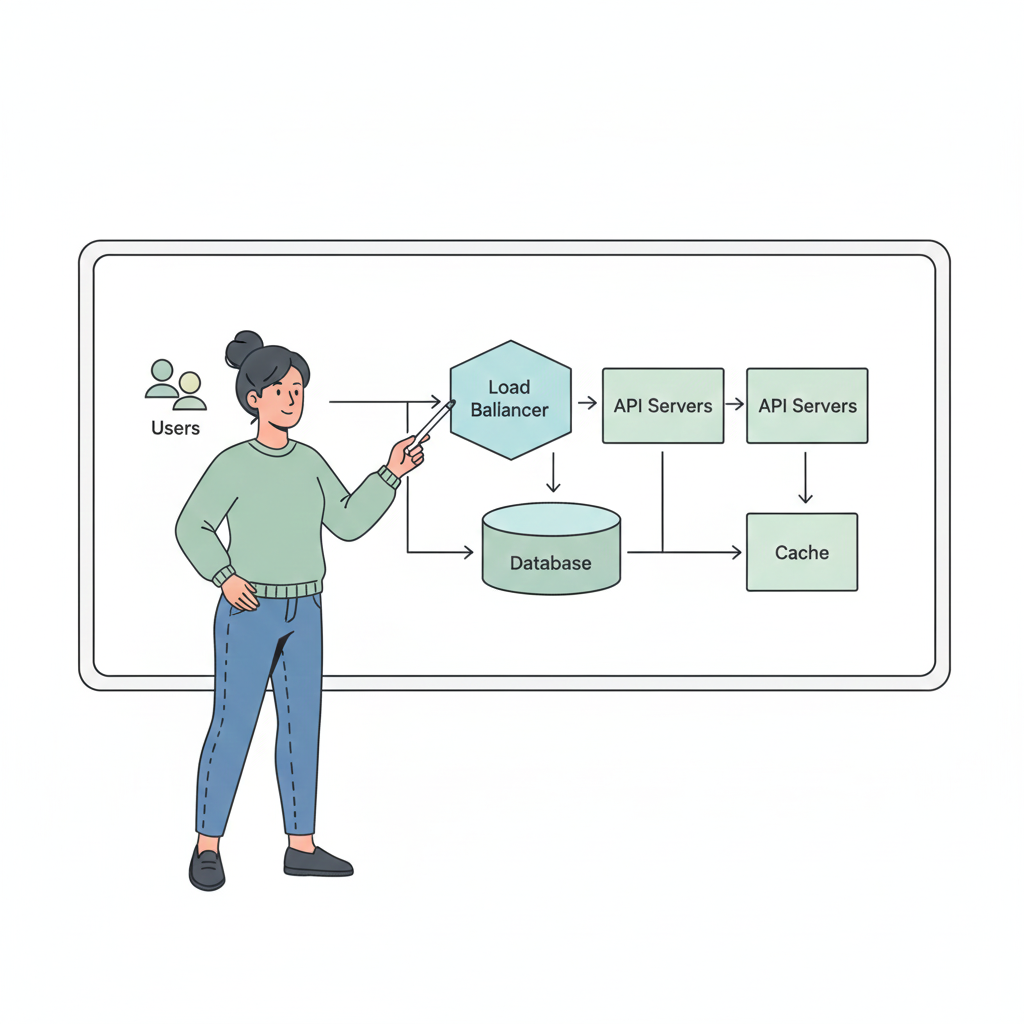
Why Stateless Services Scale Better
In stateless systems:
- Any request can be handled by any server
- No dependency on previous requests
- Failed servers don’t break user sessions
This makes stateless services ideal for:
- Cloud-native apps
- Microservices architectures
- High-traffic APIs
Real-World Example
Login Flow Using JWT:
- User logs in with credentials
- Server validates credentials
- Server issues JWT token
- Client sends JWT with every request
- Server verifies token and checks permissions
No session is stored on the server—making the system scalable and resilient.
Key Takeaways
- Authentication verifies identity
- Authorization defines permissions
- Sessions are simple but hard to scale
- Tokens (JWT) enable stateless design
- Stateless services are easier to scale and more reliable
Understanding these concepts is critical before designing microservices, APIs, or distributed systems.
What’s Next?
In the next blog, we’ll explore:
👉 Caching, Databases & Storage Basics
You’ll learn when to use caches, how databases scale, and common storage patterns.